Linux and the malwares
There are no viruses on Linux !
– A fool
You may have seen this endless urban legend in news comments regarding some vulnerabilities or malwares targeting Microsoft Windows. “Linux cannot be harmed by malwares”, “there are not viruses on Linux”, “you don’t need an antivirus on Linux”, blah blah blah. This magical spell was also spread on MacOS world because of its BSD derivative Unix foundations.
All of this is false, Unix systems and Unix-like, just like Microsoft Windows, are targeted by malwares attacks. In 2021, there was 155 vulnerabilities discovered in the Linux Kernel, showing that it’s not so invulnerable and can be targeted by a lot of possible attacks. Keep in mind that CVE database contains only the known vulnerabilities, so how many are still unknown and possibly exploited ?
The IT Security is not a question of ideology regarding which OS you use, it’s a complete value chain including good practices, constant alerting and information about your tool chain vulnerabilities. You can’t base a security policy on this kind of prejudice.
The Myth origin
One of the myth foundation is the design of the Unix systems. Since the beginning of times, they are based under a multi user principle where, normally, each process should run in its dedicated userspace with the associated limitations. A more advanced approach of this segregation is the base of process isolation like chroot and since a couple of decades, the containerization.
The apparent Linux resilience regarding malwares is globally because the infected process would not have access to the entire system and could only harm its userspace. Indeed, the super-admin user - root - is restricted to system administrators. Give this access to anybody, and your system will break because the OS considers the user root is aware of what it does.
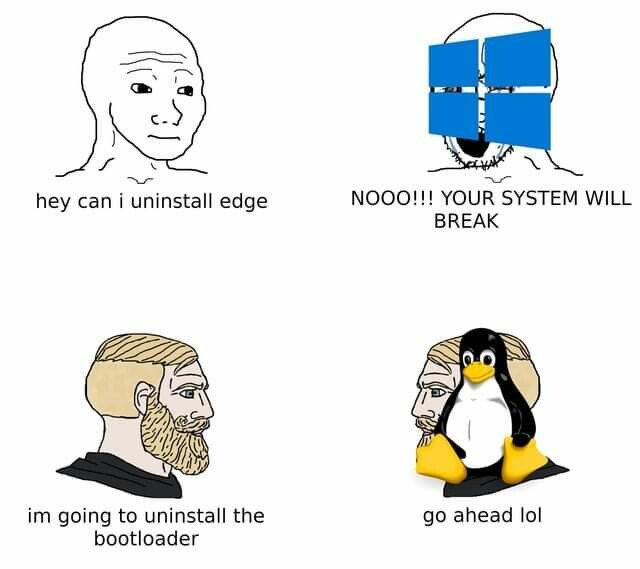
Windows thinks the user is stupid, Linux wants a proof.
– An old say
Another attributed origin is the low Linux market shares on Desktop. But this idea forget that Linux distributions are highly present on server hosting environments and this one is heavily targeted by piracy. Nowadays, the malwares are not the annoying virus that will randomly delete your files on your computer. They’re also weapons created by privates or governments interests. The IT vulnerabilities market is very prosperous and organized, there are also promotional sales for leaked e-mail or passwords databases ! On a personal note, because we cannot have a week without an IT security breach incident news, I think we are in a new cold war that runs on the networks.
Which attacks can target Linux ?
Now we’ve destroyed the prejudices, let see what can harm a Linux system.
Viruses and trojans
Because of its design, Linux is less vulnerable to usual viruses. An infected binary could not leave its userspace unless it use a privilege escalation breach. The Kernel could be temporary infected because it only reside in live memory and is read only. In case the binary works with root access, it could affect the entire system easily and spray itself.
One of the other reasons that makes the viruses and trojans not really interesting is the system package manager. Software repositories managers regularly inspect them to ensure there are no malwares on it. The binaries are checked with checksum verification and PGP signatures.
It’s still possible to attack a software repository or hijack it with a man in the middle attacks, but the package signature is still an effective protection. One of the risks is in case of a malware can modify the PGP key vault to deceive the verification process. One of the other usual protection is the reproductible build, a process where the compilation is always executed with the same parameters to ensure the produced binary is always the same.
Virus and Trojans are generally from outside origin, like manual installations of an infected binary or a non-mastered script execution. I think about the bad practice we can find in a lot of tutorials asking to execute a script like this : curl https://script-to-excute | bash. That’s a very very bad practice because you don’t known what you’re executing ! If you do this with root, it’s open bar and happy hour.
Targeted attacks
A Linux distro, it’s basically the Linux Kernel with the GNU software suite, an init system (init, systemd, etc), and a lot of softwares, tools, services, more or less complex. Distro maintainers try to be consistant with all of these layers, but this diversity of softwares and developers is also a great surface of attack.
This is the most privileged attack pattern for a Unix system and assimilated. These attacks are notably worms type.
The worms are different from viruses. A computer virus works in the same way as a biological one : it uses an host to replicated itself and execute its code, in this case, the host is a computer program. The worm is autonomous. Its an independent program that can scan for known vulnerabilities and exploit them (like privilege escalation) to spread itself.
Linux systems are globally targeted by worms because there are mostly servers. Because of this role, they expose services with ports and protocols and if they are vulnerable, they become an entry point for an attack that can use a breach and propagate itself.
The recent Log4Shell incident is a good example of a targeted attack because of a small applicative service, the entire system could be compromised with a privilege escalation.
Yes but log4j, that’s Java, not Linux !
– A desperate tentative
This is exactly what I mean : targeted attacks target an application component working on a Linux server to take the control over the whole system. The insidious part in the story is that they can (and do) use undisclosed vulnerabilities.
In a more system integrated incident, we have CronRAT which was discovered on November 2021. CronRAT is a malware that inserted itself into the crontab entries, the typical Linux scheduler, at an impossible date : February 31th. If the entry was a valid syntax, the executed code was unusable at first sight because it was encapsulated inside multiple compression layers and code obfuscation and generated random checksum values to deceive the firewalls. This malware is able to create a backdoor on the system, and it’s coded with Bash ! It was a good example of incomplete security policy of Websites where the Front is always protected but the back is neglected because not exposed.
A healthy transmitter
The other attack vector on Linux is to exploit the fact it could be a healthy transmitter. If the attack doesn’t directly target Linux, the system can still propagate it. That the reason why a file share server or a mail server running over Linux must have an antivirus to avoid spreading the infection to the clients.
One more thing ?
Just like Windows, Linux is also targeted by ransomware (these softwares that encrypt the user data and promise a decryption in exchange of a ransom - spoiler alert, that’s almost never the case). The embedded devices are also a big attack access, notably the IoT sector, because the manufacturers are usually lazy and bad in software management and keep online old versions that are completely vulnerable to known attack patterns. That’s a nice playground for attackers and botnets.
So, Linux is not better in security ?
Like I said an the beginning, because of their design, Unix and assimilated systems have a an apparent resilience to usual attacks inflicted in the Microsoft world. However, if Windows had a bad habit to create a user account with too much privileges, this issue is gone since a while as there are now far more privilege escalation mechanisms than before in the Microsoft system.
A Linux-based system has the same risks as a Windows because the attacks patterns are likely the same with privilege escalation and vulnerability exploitation, or because the system is badly setup. And don’t forget the softwares that are not maintained and contains a lot of known vulnerability that are still running.
So, no, unlike the old troll always repeat, “Linux” is as targeted by malwares as the others systems. The surface and patterns can be different, but there are the same risks if the system is badly configured or maintained. The big part of the problem is when you think you’re invulnerable, the security will be assuredly neglected.
What can we do to have a secured Linux installation ?
As I’m not an IT security expert, I don’t have the exhaustive answer. However, here is a list of good practice you can use :
- Less privilege principle : a human or applicative user must only have the required permissions to work, no more. The filesystem permissions must also be consistant (yes, I’m talking to you, the
chmod 777adept) - Secure your network with firewalls : what is not explicitly allowed is forbidden.
- Complement : advanced firewalls can block protocols and domains. For instance, you can block the HTTPS protocol if the port is listened by a service that not using this protocol.
- Avoid having active and unused services listening on public ports
- Complement : avoid using standard ports, there are the first targeted
- Always be up to date in your system, softwares and dependencies
- Restrict root access : no ssh connection, usable only by identified users
- Do not disengage security mechanisms (SELinux in Enforcing mode, Firewalld active, etc)
- Use complexe and regularly changed passwords
- Always encrypt your data and communications
- Have an antivirus
- Being a little paranoid and see the evil everywhere 😅
If you want to try a secured Linux installation, I recommend you the ANSSI (French national agency for IT systems security) guide.
But yes, as you can see, Linux and Unix system are not magically better in security than the others.
I hope this article helped to break an old myth which is completely wrong and can trigger bad behaviors because of a counter productive false security feeling.